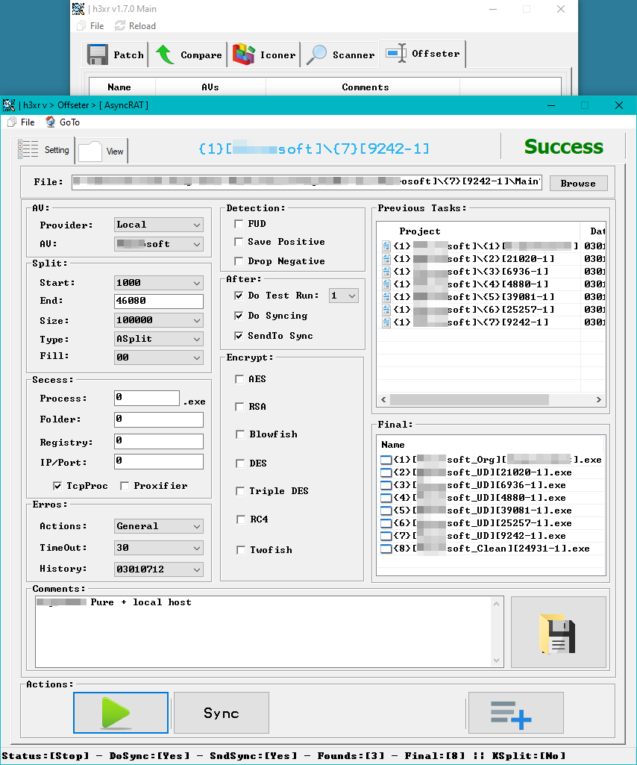
h3xr is tool offers a robust interface for analyzing, patching, and synchronizing applications. The main functionalities of the tool are next:
- Patch, Compare, Iconer, Scanner, Offsetter:
- The primary interface provides options to patch files, compare versions, manage icons, scan for anomalies, and offset binary data for deeper analysis.
- Project Management:
- The tool allows users to manage multiple projects at same time, displaying a list of previous tasks with detailed project IDs, names, and timestamps.
- Analysis Unit (AU) Configuration:
- Users can configure the Analysis Unit (AU) by selecting providers and specifying analysis parameters. The AU settings include options to split files by setting start and end points, defining the size and type of splits, and filling parameters.
- Detection and Post-Processing:
- Detection settings include options to flag potentially unwanted programs (PUPs), save positive detections, and drop negatives. Post-processing settings include running test executions, syncing files, and sending results to synchronization.
- Encryption Options:
- The tool supports multiple encryption methods such as AES, RSA, Blowfish, DES, Triple DES, RC4, and Twofish, ensuring secure handling of data during analysis.
- Success and Error Handling:
- The tool tracks the success of processes, folders, registry entries, and IP/Port configurations. It also manages errors with customizable actions, timeouts, and history logging.
- Comments and Actions:
- Users can add comments for clarity and documentation. The action buttons allow users to start processes, sync data, and manage tasks efficiently.
This ethical hacking tool is designed solely for educational purposes. It is intended to be used only by official agencies and authorized personnel. Unauthorized use of this tool is strictly prohibited and may result in legal consequences. To obtain your exclusive copy of h3xr, kindly reach out to us.